2021/02/20
Introduction
In this blog post, I'll be detailing how you can exploit the "Guest Network" feature of your Ubiquiti Unifi AP to act as a VLAN-like isolated network for your IOT devices. This is by far not the most elegant solution for isolating clients from your network, and you should only follow the instructions shown here if your router doesn't support VLANs, or if you can't use them for any other reason.
However, if you're in the following situation, do follow along...
- You have some IOT devices, probably from a well-known Chinese marketplace, which you don't trust on your network
- You wish to isolate your IOT devices from the rest of your LAN
- You wish to cut off your IOT devices from the internet
- Your router doesn't support VLAN networks
- Your router doesn't support firewall rules
- You have Ubiquiti APs, but you don't want to buy an expensive Ubiquiti router
- Your can't replace your router easily because your ISP is terrible
Inspired by this post on the Ubiquity forums, I set out to try to use the Guest Network feature on Ubiquiti APs to block certain clients from connecting to the internal network.
Creating the Guest Network
Log into your Unifi Network Controller software. In the Settings, create a new WiFi Guest Hotspot. Don't create a new Network. If your router does not support VLAN tags, it will simply assign your IOT devices an IP within your main subnet anyway, defeating the entire purpose of your isolated network. In addition, you wouldn't be able to define firewall rules anyway because you need an Ubiquiti router to define those in the controller software.
Give your network a name and a password. Enable the toggle "Guest Portal" and enable Authentication. I've chosen the Voucher authentication, but any other form of authentication will likely work too. It's important that you have some form of authentication, because if you don't, clients immediately gain internet access, which is what we want to avoid. By defining an authentication method (and not giving the client any way to authenticate), we effectively block internet access for all clients on the Guest Network. This replicates the behaviour of WAN firewall rules, but without the firewall.
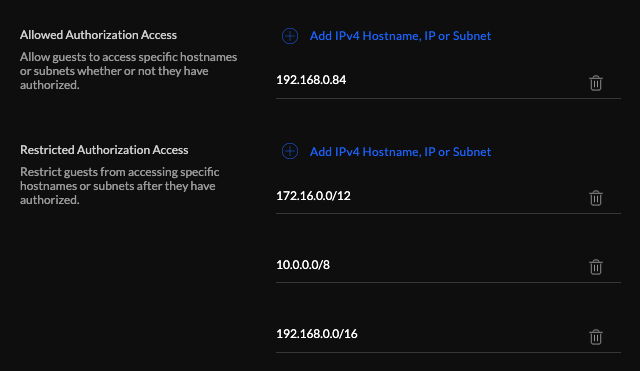
We still want our IOT gadgets to be able to talk to our central IOT command server, for example a Raspberry Pi running Home Assistant. Under "Allowed Authorization Access", enter the IP address of your command server. Of course, this means you should've set up a static IP for that server. Under "Restricted Authorization Access", make sure to enter the subnet of your local network. This ensures that your IOT devices won't be able to talk to other devices on the network, like your printer or your Plex server, and replicates LAN firewall rules.
Finally, save your network. You can test your configuration by using your laptop or your phone to connect to the IOT network. If you can't go online or ping other devices on your local network, but you can reach your command server, you've set up everything correctly!